L'actualité de l'innovation
Bienvenue sur le site de la recherche et de l'innovation d'Orange
E-Reo donne une vie numérique aux langues autochtones
Lire l'article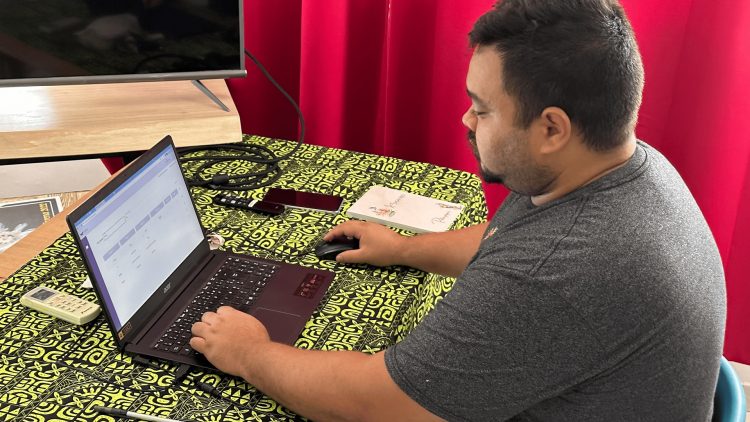

 Découvrir
Découvrir  Explorer
Explorer  Approfondir
Approfondir 








